What Is a DApp Frontend?
A DApp frontend is a typical web or mobile interface that interacts with on-chain smart contracts. It:
Loads HTML, CSS and JavaScript in the user’s browser
Invokes wallet extensions (e.g., MetaMask) via libraries like Ethers.js or Web3.js
Fetches data either directly from the blockchain or via RPC endpoints
Without proper safeguards, each of these steps can enable attackers to tamper with your code, mislead users, or leak sensitive data, as outlined in the MDN Web Security overview .
Core Frontend Development Steps
Before diving into risks, it helps to understand the typical flow of a DApp frontend:
Set up your toolchain (e.g., React, Vue, Next.js)
Integrate blockchain libraries ( MetaMask , WalletConnect documentation )
Write UI components that read from and write to smart contracts
Configure off-chain services or APIs to display historical data
Deploy static assets to CDNs or IPFS
Each layer—from your React components down to the CDN—carries its own set of threats.
Step | Description & Risks |
|---|---|
🛠️ Set up your toolchain | Note: Choose frameworks (React, Vue, Next.js). |
🔗 Integrate blockchain libraries | Note: Connect with MetaMask, WalletConnect, etc. |
🧩 Write UI components | Note: Build interfaces to interact with smart contracts. |
📊 Configure off-chain services | Note: Fetch and display historical or external data. |
🚀 Deploy static assets | Note: Host frontend on CDNs or IPFS. |
Technical Risks: Security and Integrity
Wallet Extension Vulnerabilities
Browser wallets can be compromised, hijacked, or spoofed:
Malicious extensions masquerading as MetaMask clones can capture private keys. ( ZDNet report )
Supply-chain attacks on wallet updates may inject unauthorized code, as seen in dependency confusion and supply chain attacks on npm packages .

Code Tampering During Delivery
If your frontend is hosted on a CDN or third-party server, a compromised node could inject malware into your JavaScript bundle. This form of code tampering is classified as security misconfiguration by OWASP Top Ten . A man-in-the-middle attacker might alter RPC endpoints or transaction parameters before they reach the user’s wallet.
Replay Attacks and Transaction Resubmission
Without strict nonce management, a transaction signed once can be broadcast multiple times. Attackers can:
Resubmit stale transactions to drain funds
Alter transaction data if your UI doesn’t verify the on-chain state before signing ( Chainlink blog on replay attacks )
User Experience and Inclusion Hazards
Unclear Consent and Misleading UI
If you don’t clearly display transaction details—recipient address, token amount or gas fees—users might unknowingly authorize malicious transfers. “Popup fatigue” can lead people to click through dangerous prompts. ( Chainalysis 2022 report )
Accessibility and Inclusivity Risks
Many DApp frontends overlook screen-reader compatibility, keyboard navigation or color-contrast standards. That not only excludes users with disabilities but can violate WCAG guidelines and related regulations.
Operational and Compliance Exposures
Centralized Infrastructure Dependencies
Relying on a single RPC provider or API undermines decentralization. If that provider is taken offline or is pressured to censor transactions, your DApp effectively replicates the centralized model you intended to avoid, as demonstrated during the Infura outage and Ethereum network issues .
Analytics, Tracking, and Data Leakage
Frontends often import Google Analytics or third-party chat widgets that can capture IP addresses, wallet addresses or user behavior. Inadvertent data collection could violate privacy laws like GDPR or UK data protection regulations .
Localization and Translation Mistakes
Poorly translated labels or numeric formats may confuse users into approving incorrect values. An attacker could exploit this by intercepting locale files and swapping decimal separators, tricking users into oversized transactions.
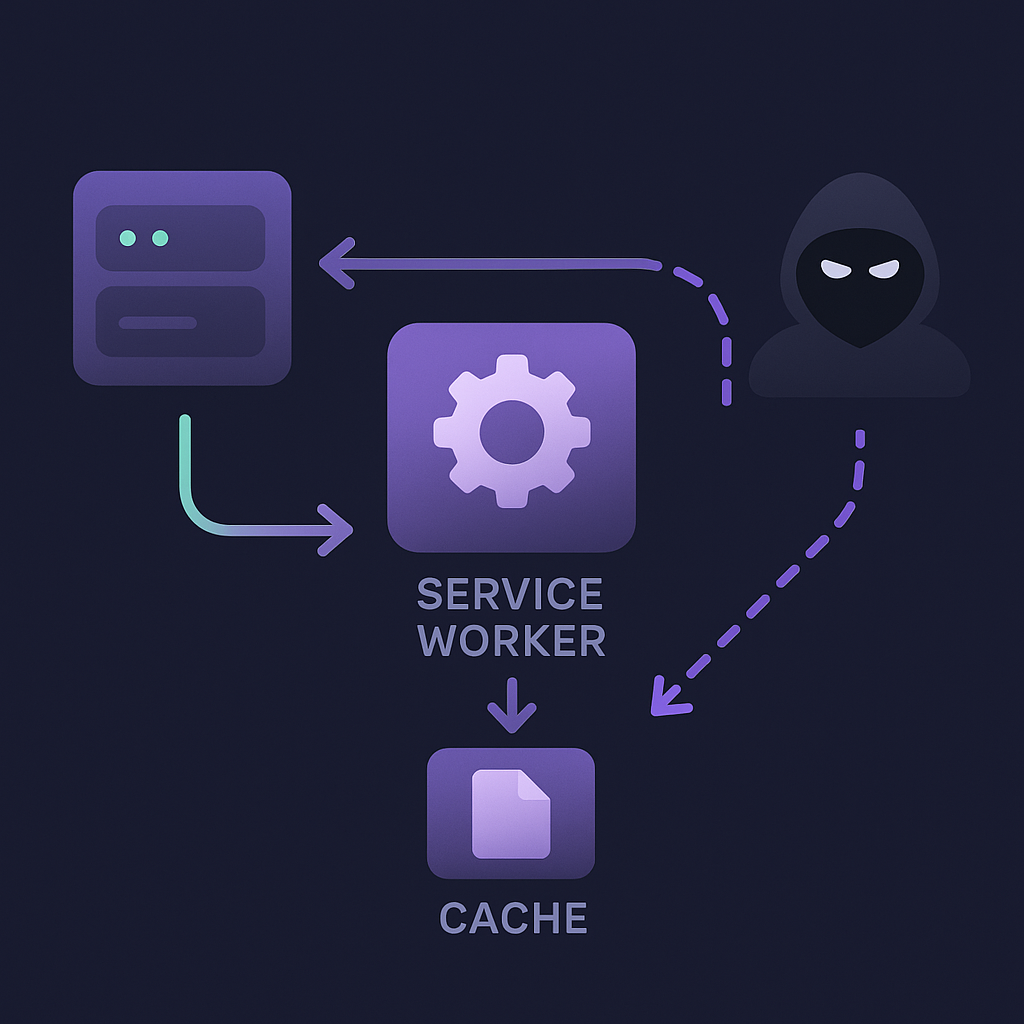
Progressive Web App (PWA) Vulnerabilities
PWAs bring offline support and background sync to DApps, but service workers can cache sensitive data or be hijacked:
Stale cache entries may serve outdated contract ABIs
A rogue service worker script can intercept fetch requests and exfiltrate data ( service worker cache security considerations )
Wrapping It All Up
Your DApp frontend is as critical as the smart contract layer. By understanding these technical, UX and compliance risks, you can put robust checks in place—from code-integrity monitoring and clear transaction prompts to decentralized RPC fallback strategies and automated accessibility tests. Address these areas, and you’ll build a frontend that’s not just user-friendly, but truly secure and resilient.
Need a Frontend Team?
Book a free consult from expert frontend dev team with Blockchain expertise
Book a Meet:format(webp))
:format(webp))
:format(webp))
:format(webp))